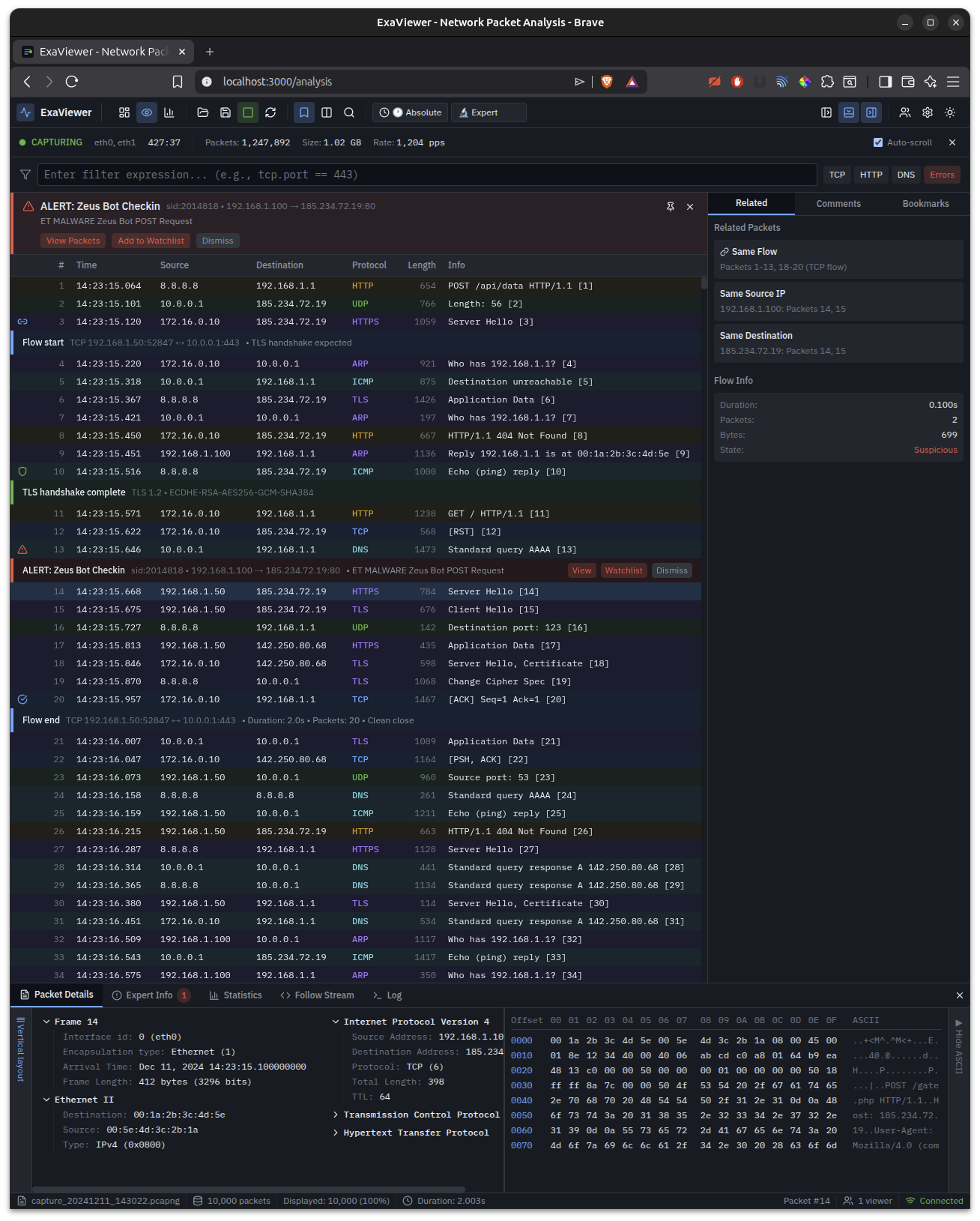
Packet analysis with inline IDS alerts, flow markers, bookmarks, and hex dump. Detecting Zeus Bot C2 communication in real-time.
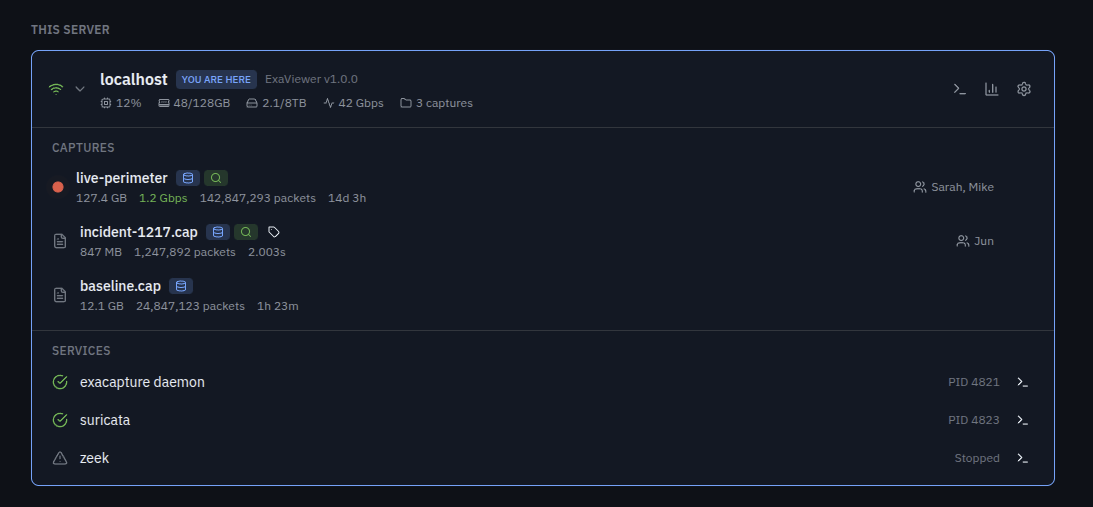
Fleet dashboard with server discovery, capture management, performance metrics, and integrated Suricata/Zeek services.

Live performance monitoring — packet rate, bandwidth, per-core CPU, protocol distribution, top talkers, and recent alerts.