Capture at Scale.
24/7.
Enterprise capture daemon for persistent, high-volume packet recording at the network edge. Captures, indexes, and analyzes inline. Serves multiple analysts simultaneously. The packets never leave the server.
Enterprise capture daemon for persistent, high-volume packet recording at the network edge. Captures, indexes, and analyzes inline. Serves multiple analysts simultaneously. The packets never leave the server.
Clean separation. One captures and serves. The other analyzes and displays.
ExaCapture captures, indexes, analyzes, and serves. For petabyte-scale captures, post-hoc analysis isn't practical. The analysis must happen during capture.
Sustained high-rate capture without packet loss. Built on jNetWorks with DPDK kernel-bypass and Napatech SmartNIC support. Line-rate on every port.
As packets arrive, ExaCapture builds flow tables, protocol statistics, and timestamp indexes. When you need to find something, you query — you don't scan.
Protocol dissection, analysis token generation, anomaly detection, and IDS integration — all at capture time. You can't re-analyze a year of traffic after the fact.
Capture at maximum throughput with minimal processing, then run analysis passes during off-peak hours. Capture files track what processing has been applied.
Every capture session enforces security levels 0–20. Different analysts see different views of the same data based on clearance. Obfuscation happens at the source.
ExaCapture is a daemon. It runs continuously and serves packet data to any authorized ExaViewer client. Five analysts viewing the same live capture simultaneously.
ExaCapture generates analysis tokens inline with packet capture — flow boundaries, protocol events, IDS alerts, anomaly markers. These tokens are stored alongside the raw packets.
When ExaViewer connects, it reads existing tokens rather than re-analyzing. For small captures, this is a convenience. For petabyte-scale captures, it's essential.
Capture files track what processing has been applied — indexed, analyzed, tagged — so analysts always know what they're working with.
-- Raw packets with inline tokens Packet 1 10.0.0.1 → 8.8.8.8 DNS Packet 2 10.0.0.1 → 185.234.72.19 TCP SYN [Token: Flow Start tcp:10.0.0.1:443] Packet 3 185.234.72.19 → 10.0.0.1 SYN-ACK Packet 4 10.0.0.1 → 185.234.72.19 ACK [Token: TLS Handshake Complete] [Token: ECDHE-RSA-AES256-GCM-SHA384] Packet 5 10.0.0.1 → 185.234.72.19 POST [Token: Alert sid:2014818] [Token: ET MALWARE Zeus Bot POST] -- ExaViewer renders tokens instantly -- No re-analysis needed
Console for scripting and automation. Terminal for constrained environments. Web dashboard for visual management. Same capabilities, different access patterns.
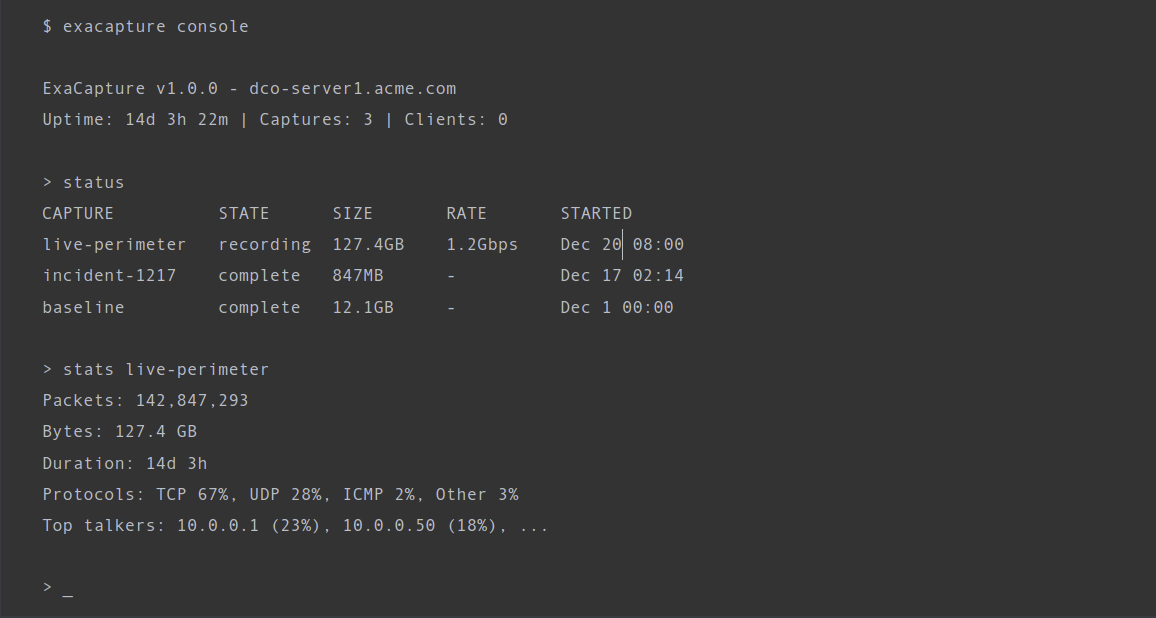
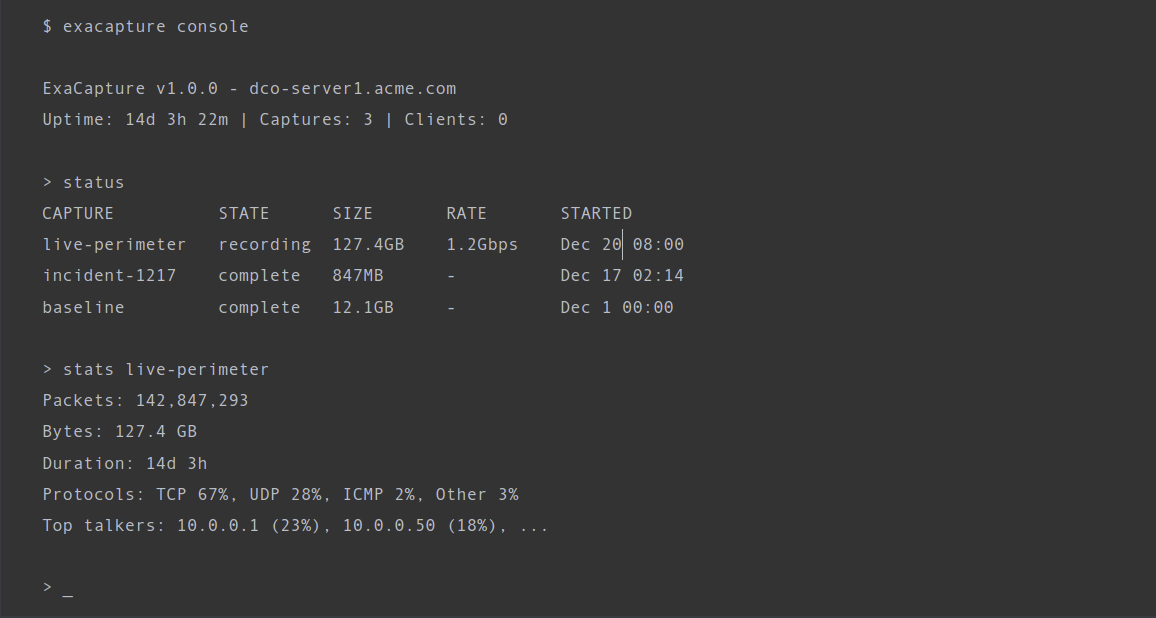
$ exacapture console ExaCapture v1.0.0 - dco-server1.acme.com Uptime: 14d 3h 22m | Captures: 3 | Clients: 2 > status CAPTURE STATE SIZE RATE CLIENTS live-perimeter recording 127.4GB 1.2Gbps Sarah, Mike incident-1217 complete 847MB - Jun baseline complete 12.1GB - - > stats live-perimeter Packets: 142,847,293 Bytes: 127.4 GB Duration: 14d 3h Protocols: TCP 67%, UDP 28%, ICMP 2%, Other 3% Top talkers: 10.0.0.1 (23%), 10.0.0.50 (18%), ... > start incident-0225 --interface eth0 --filter "not port 22" Capture started: incident-0225 on eth0 > clients USER CAPTURE CONNECTED SECURITY Sarah live-perimeter 2h 15m Level 5 Mike live-perimeter 45m Level 5 Jun incident-1217 3h 02m Level 3 > _
Full command-line interface for scripting and automation. Start and stop captures, check status, view statistics, manage connected clients, configure retention policies. SSH in from anywhere. Pipe output to monitoring systems.
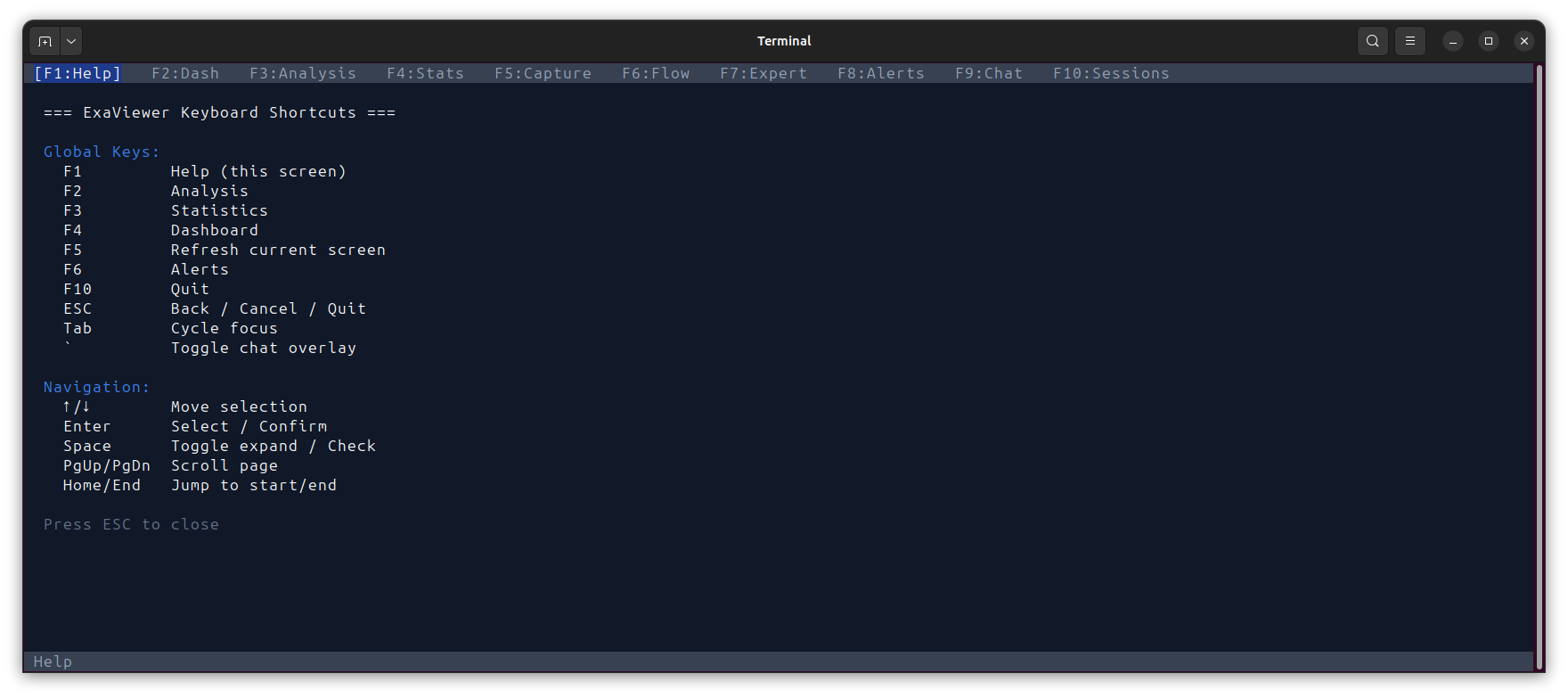
Visual TUI for slow connections or constrained environments. F-key navigation between views. Live updating statistics, capture status, and alert feeds. All management capabilities accessible without a browser.
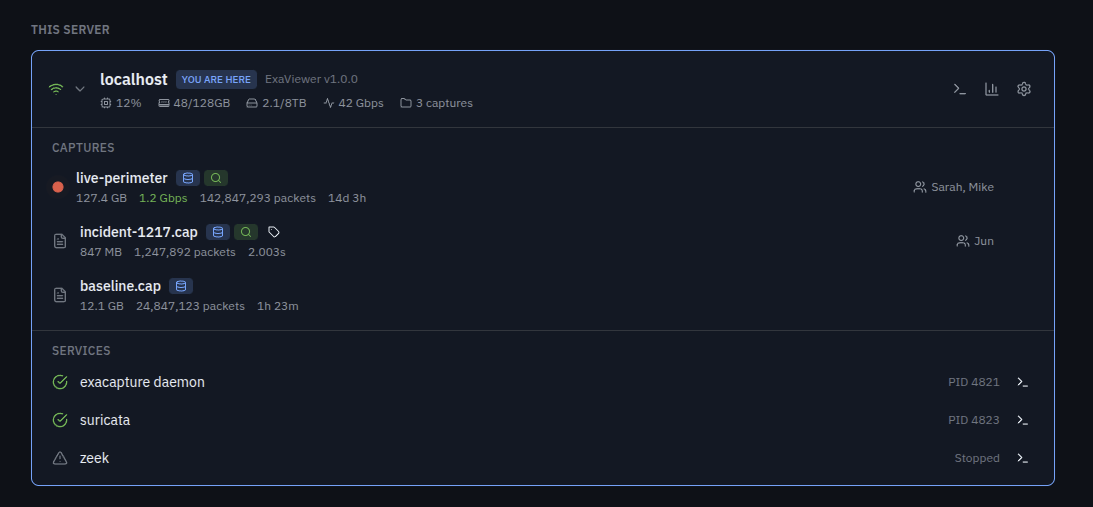
React-based management interface. Server status, capture management, performance metrics, connected clients, and service integration. Connect via browser directly or through SSH tunnel. Shows status — not packets.
ExaCapture and ExaViewer share the same dashboard, the same discovery protocol, the same security model. Two products, one architecture.
THE WORKFLOW THAT ACTUALLY WORKS It's 2am. Incident response. Capture is on a server in a datacenter. Your team is in three time zones. Old way: Download 50 GB. Wait. Upload to cloud. Wait. Everyone downloads. Someone's VPN breaks. An hour gone before anyone sees packets together. New way: $ exaviewer mark@dco-server1:incident-1217 You're in. Packets streaming. Sarah in London joins. Mike in Austin. Same data. Same view. Real-time. No downloads. No uploads. No cloud. The packets never leave the server.
Open either product. You see the same dashboard. The same discovered servers. The same captures with processing badges showing what's been indexed, analyzed, and tagged.
In ExaCapture, clicking a capture shows management options — permissions, retention, processing status. In ExaViewer, clicking the same capture opens the analysis view with full packet data.
Same dashboard. Same resource visibility. Different capabilities based on context.
Both products discover each other automatically. Localhost is always checked with zero configuration. LAN multicast probe for trusted networks. Manual server list for WAN, VPN, or cloud deployments. Your entire capture infrastructure visible from one place.
Obfuscation happens at ExaCapture before data is transmitted. You can't see what you're not cleared for. Period.
| Analyst | Security Level | What They See |
|---|---|---|
| Senior Analyst | Level 5 | Full packet data, all payloads, all metadata |
| Junior Analyst | Level 3 | Packets with payload content obfuscated |
| External Consultant | Level 1 | Metadata only — protocols, timing, sizes |
Granular security from Level 0 (no enforcement, standalone use) through Level 20 (air-gapped, two-person integrity, hardware tokens).
Automatic detection and obfuscation of PII, IMSI, IMEI, credit card numbers, and other sensitive data. Policy-driven, not manual.
AES-256-GCM encryption for stored captures. Policy-driven key management. Captures are protected from the moment they hit disk.
ExaCapture integrates with Suricata and Zeek natively. IDS alerts are captured as analysis tokens alongside packets, so when an analyst opens a capture in ExaViewer, alerts appear inline in the packet list with full context.
No separate tools. No context switching. No correlating timestamps across different log files. The alert is right there, next to the packet that triggered it.
Suricata rule compatibility means your existing rulesets work immediately. Zeek logs are ingested as structured metadata.
> services SERVICE STATE PID exacapture daemon running 4821 suricata running 4823 zeek stopped - > suricata status Rules loaded: 48,293 Alerts (24h): 127 Last alert: 3m ago sid:2014818 ET MALWARE Zeus Bot POST 10.0.0.1:49152 → 185.234.72.19:80 > suricata rules reload Reloading Suricata rules... Rules loaded: 48,307 (+14 new) > _
# Install $ apt install exacapture # Start as daemon (systemd) $ systemctl enable exacapture $ systemctl start exacapture # Or start manually $ exacapture start \ --interface eth0,eth1 \ --output /captures/ \ --retention 90d \ --security-level 5 # Check status $ exacapture status ExaCapture v1.0.0 - running Uptime: 14d 3h 22m Captures: 3 | Clients: 2 Disk: 2.1/8 TB (26%) # Enter interactive console $ exacapture console
Install the package. Start the daemon. ExaCapture runs as a systemd service with automatic restart, log rotation, and health monitoring.
Configuration via YAML config file or command-line arguments. Prometheus metrics endpoint for integration with your existing monitoring infrastructure.
Deploy on your datacenter tap. Your cloud gateway. Your SOC sensor. ExaCapture runs continuously without human intervention. When something happens, the data is already there.
ExaViewer ExaCapture View and analyze Capture and index Perpetual license Subscription per server │ │ └────────────┬────────────┘ │ Same dashboard Same discovery Same security model Same analysis tokens │ ▼ ExaScale OS (2026) Federate and scale Exabyte-scale capture Global cluster management
Start with ExaViewer and local files. Add ExaCapture when you need persistent infrastructure. Scale to ExaScale OS when you're managing petabytes across continents.
Schedule a demo or talk to our team about deployment.